Insider Brief
- A new analysis finds that 128-bit symmetric encryption, such as AES-128, is likely to remain secure against quantum attacks due to practical limits on quantum algorithms like Grover’s.
- The study shows that exploiting Grover’s algorithm at scale would require an impractically large number of quantum systems and computational resources, far beyond current or near-term capabilities.
- The findings indicate that quantum risk is expected to emerge first in public-key cryptography, while symmetric encryption does not require immediate changes in the post-quantum transition.
Quantum computers are unlikely to weaken today’s widely used symmetric encryption, according to a new analysis that challenges a common assumption about quantum threats and suggests security efforts should focus elsewhere.
A blog post by cryptography researcher Filippo Valsorda finds that 128-bit symmetric keys, such as those used in AES-128, remain effectively secure even in the presence of large-scale quantum computers, due to — theoretically — practical limits on how quantum algorithms operate in real-world systems.
The finding runs counter to a widespread belief that quantum computing will “halve” the strength of symmetric encryption, forcing a shift to longer keys. Instead, the analysis indicates that this interpretation misapplies the theoretical speedup of quantum search algorithms and overlooks engineering constraints that sharply limit their impact.

The result, if confirmed, has direct implications for cybersecurity planning as governments and industry move to replace vulnerable public-key cryptography with post-quantum alternatives. It suggests symmetric cryptography—used in everything from encrypted messaging to data storage—may not require the same urgency.
Public-key cryptography is used to exchange secrets, while symmetric encryption protects the data itself. The researcher finds the latter remains largely unaffected.
Understanding the Quantum Threat
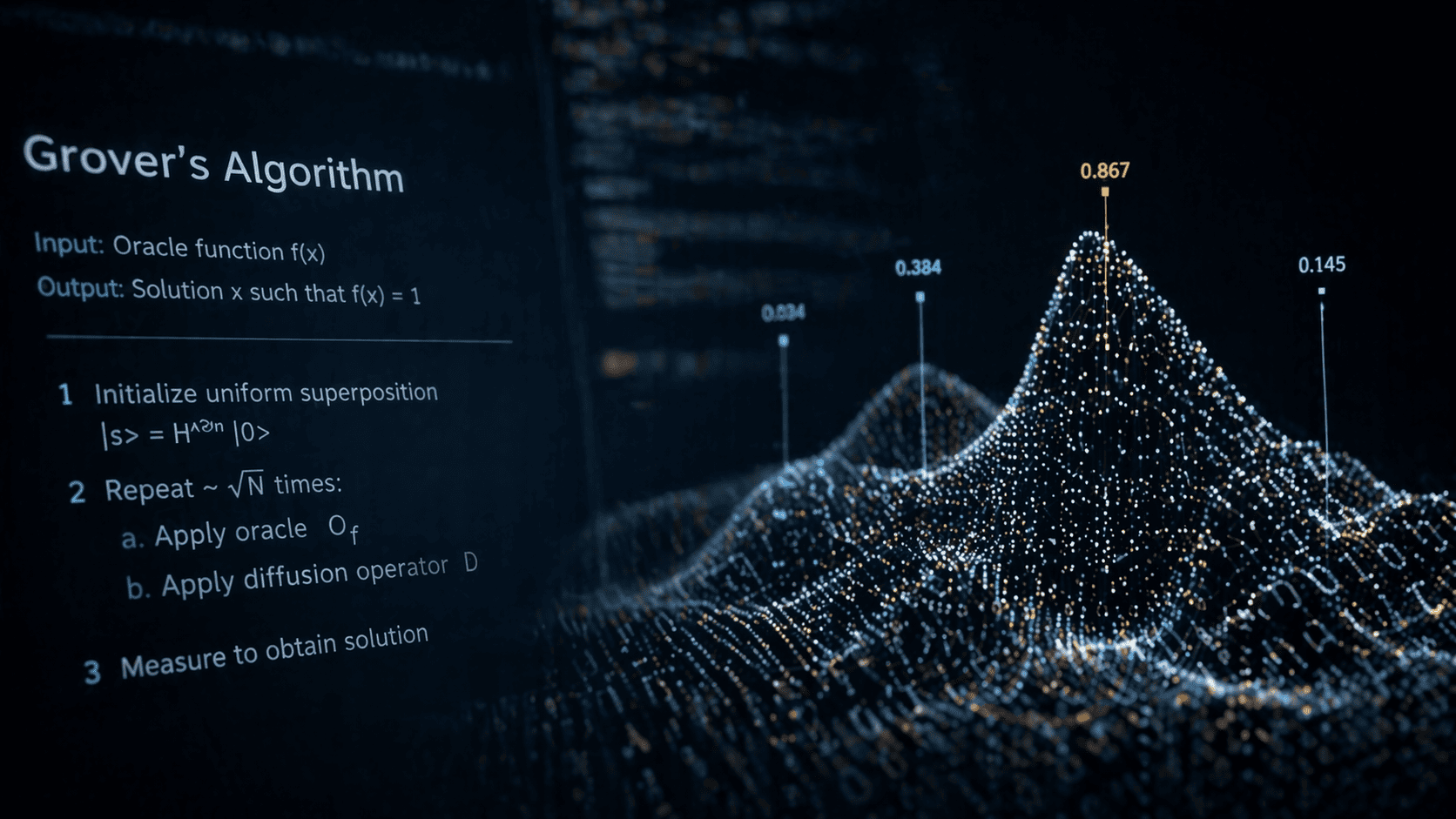
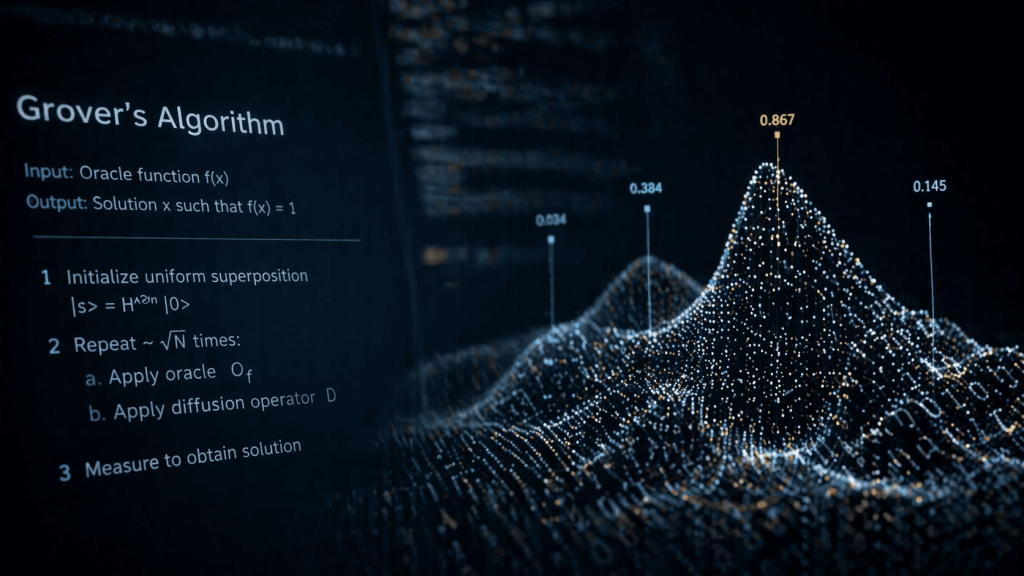
The concern stems from a quantum algorithm known as Grover’s algorithm, which can search large datasets faster than classical methods. In theory, Grover’s offers a quadratic speedup, meaning a brute-force attack on a 128-bit key could require roughly 2⁶⁴ operations instead of 2¹²⁸. In common language (or maybe not), that means it would require about 18 quintillion operations instead of roughly 340 undecillion.
That apparent reduction has led some analysts to argue that symmetric key sizes should double to maintain the same level of security in a quantum era. Valsorda disputes that conclusion, however, making the argument that that Grover’s algorithm is fundamentally constrained by its need for sequential execution. What this means is Grover’s algorithm works by repeatedly applying a sequence of operations that build on each other.
According to the post, unlike classical brute-force attacks, which can be easily parallelized across many processors, Grover’s cannot be efficiently split across multiple quantum machines without losing much of its advantage.
In classical computing, dividing a search problem among many machines reduces the time required without increasing the total computational effort. In quantum computing, dividing the problem reduces the benefit of the algorithm itself, increasing the total work needed across the system.
As a result, the theoretical speedup becomes far less meaningful in practice.
Quantifying the Cost
To test whether Grover’s algorithm poses a realistic threat, a model of a hypothetical attack on AES-128 is used with optimistic assumptions about future quantum hardware.
The analysis assumes a high-performance quantum system capable of executing operations at microsecond speeds and running continuously for a decade without interruption—conditions that exceed current capabilities.
Even under those assumptions, the attack would require on the order of 2⁴⁷ — about 140 trillion — parallel quantum systems, each running complex circuits involving hundreds of logical qubits.
In total, the computational cost is estimated at approximately 2¹⁰⁴.⁵ — let’s just say an astronomically large number — of operations when accounting for both circuit depth and width, a metric analogous to total processing work in classical systems.
By comparison, recent estimates suggest that breaking widely used public-key cryptography with a different quantum algorithm, called Shor’s algorithm, would require far fewer resources, on the order of tens of millions of quantum operations.
According to the post, attacking AES-128 with Grover’s would be massively more expensive than breaking elliptic-curve cryptography, by a factor of roughly 2⁷⁸.⁵, or about 400 sextillion.
The gap suggests quantum computers are likely to threaten public-key systems well before they pose a practical risk to symmetric encryption. That makes public-key cryptography the nearer-term concern.
Alignment With Standards
The conclusions align with positions taken by major standards organizations, including the National Institute of Standards and Technology (NIST), according to the post.
NIST has explicitly stated that AES-128 remains secure in a post-quantum context and continues to use it as a benchmark for defining security levels in its post-quantum cryptography framework.
The agency’s guidance reflects Valsorda’s assertions that while Grover’s algorithm offers a theoretical speedup, its requirement for long, uninterrupted sequences of quantum operations limits its practical effectiveness.
NIST also emphasizes that real-world attacks rely on parallel processing, which further reduces the advantage of quantum search algorithms.
Other organizations, including Germany’s Federal Office for Information Security, have reached similar conclusions, continuing to recommend AES-128 alongside longer key variants.
Implications for Post-Quantum Migration
The findings come as governments and companies accelerate efforts to transition to post-quantum cryptography, driven by concerns that quantum computers could eventually break current public-key systems.
That transition focuses primarily on replacing algorithms used for key exchange and digital signatures, such as RSA and elliptic-curve cryptography, which are vulnerable to Shor’s algorithm.
Valsorda writes that extending this transition to symmetric cryptography would be unnecessary and potentially counterproductive.
Updating symmetric key sizes would require changes across a wide range of systems, including communication protocols, hardware implementations, and software libraries. These changes could introduce compatibility issues and consume resources that might be better directed toward addressing more urgent vulnerabilities.
The analysis frames this as a coordination problem. Adopting unnecessary changes might risk fragmenting standards and complicating interoperability without improving security.
In contrast, leaving symmetric cryptography unchanged allows organizations to focus on the parts of the system that are genuinely at risk.
Methods
Valsorda relies on a combination of theoretical analysis and resource estimation to build the conclusions.
It models the performance of Grover’s algorithm using recent advances in quantum circuit design, including optimized implementations of AES within quantum systems.
Key parameters include circuit depth — or, the number of sequential operations required — and circuit width, which reflects the number of qubits operating in parallel.
The analysis also introduces a practical constraint known as maximum depth, representing the longest sequence of operations a quantum computer can execute reliably. This limit is driven by factors such as error rates, decoherence, and system stability.
By combining these parameters, the analysis estimates the minimum level of parallelization required to complete an attack within a given time frame, and the total computational cost across all systems.
The post recognizes some limitations. First, it relies on assumptions about future quantum hardware, including error-corrected systems capable of sustained operation over long periods. While these assumptions are conservative, actual implementations may differ.
The analysis also focuses on known quantum algorithms and does not account for the possibility of future advances that could change the landscape. However, the analysis does address this by noting that Grover’s algorithm has been extensively studied, and there is limited room for improvement in its core performance characteristics.
Finally, the resource estimates do not fully account for the overhead of quantum error correction, which is expected to significantly increase the physical resources required to implement logical qubits. Including these factors would likely further increase the cost of quantum attacks.
Future Work
The findings point to several areas for future research. For example, the post suggests that refining resource estimates for quantum algorithms, particularly as new hardware architectures and error-correction techniques emerge. Another idea is to improve the understanding of how quantum and classical systems interact in hybrid attack scenarios, where quantum algorithms are used alongside classical computing resources.
The study also highlights the need for clearer communication within the cybersecurity community. Misinterpretations of quantum algorithms can lead to misplaced priorities, with organizations focusing on theoretical risks rather than practical ones.
As quantum computing continues to develop, distinguishing between credible threats and speculative concerns will be critical for effective security planning.
Valsorda’s post is quite technical and this summary story may miss some of the key points within that technical data. Please read the post for deeper detail. Also, the post — nor this article itself — can be considered peer-reviewed publications. Peer-review is an important step in the scientific method and allows for research to be better vetted.