Insider Brief
- “Harvest now, decrypt later” refers to attackers collecting encrypted data today to decrypt it in the future using quantum computers.
- The threat primarily targets long-lived sensitive data such as government, financial, healthcare, and blockchain records.
- The risk is already active, making early migration to post-quantum cryptography necessary to prevent future data exposure.
Adversaries are collecting encrypted data right now. They cannot read it yet. But they do not need to because their strategy involves intercepting communications, storing them, and simply waiting. When quantum computers become powerful enough to break today’s encryption, that archived data will potentially become readable.
This is known as “harvest now, decrypt later,” and according to official warnings from the NSA, CISA, and NIST, it is already happening.
How the Attack Works
The attack unfolds in three stages, often spanning years or decades.

Adversaries begin by intercepting encrypted data through network monitoring, compromised endpoints, or data breaches. Encrypted communications, financial transactions, medical records, and government documents all get collected. Because current encryption cannot be broken efficiently with classical computers, attackers do not attempt decryption. They archive the data and move on.
Storage is cheap. At commodity prices, a petabyte of hard drive space costs under $20,000 – though enterprise-grade archival storage, with redundancy, power, and cooling, runs considerably higher. State-level actors operate data centers built specifically to house intercepted communications. The NSA’s Utah Data Center, completed in 2014, has been widely reported as designed for store massive volumes of data for exactly this purpose, though its precise capacity and purpose remain classified.
The data sits in storage, sometimes for years. Nothing active happens during this phase, which makes detection nearly impossible. Finally, when quantum computers capable of running algorithms like Shor’s become available, attackers decrypt the stored data. Information that was secure when transmitted becomes readable. By the time the breach becomes apparent, the damage is irreversible.
Who is at Risk
Not all data retains value long enough to justify this strategy. Attackers target information with extended confidentiality requirements.
Government agencies manage classified communications, diplomatic cables, intelligence archives, and national security data that remain sensitive for decades. A classified document intercepted in 2025 may still be strategically valuable in 2035.
Healthcare organizations store patient records, genomic data, and clinical research that carry lifetime confidentiality obligations. Medical information intercepted today could be used for identity theft or targeted harassment a decade from now.
Financial institutions handle transaction histories, trading algorithms, regulatory filings, and client communications. Decrypted financial data could enable market manipulation, fraud, or competitive intelligence gathering long after the original transmission. A merger negotiation recorded in 2026 might still provide actionable intelligence in 2034.
Cryptocurrency and blockchain networks face unique exposure. A Federal Reserve study warns that distributed ledgers like Bitcoin are particularly vulnerable because their entire transaction histories are public, permanent, and based on cryptography that quantum computers could eventually break. Unlike traditional databases, blockchain records cannot be deleted or retroactively encrypted.
Supply chain and procurement systems face similar exposure. A recent apexanalytix report warns that supplier invoices, payment information, commercial contracts, pricing terms, banking details, and compliance records protected by current encryption standards could all be retroactively exposed years from now, putting historical communications and proprietary information at risk.
According to NIST’s transition guidance, “encrypted data remains at risk because of the ‘harvest now, decrypt later’ threat in which adversaries collect encrypted data now with the goal of decrypting it once quantum technology matures. Since sensitive data often retains its value for many years, starting the transition to post-quantum cryptography now is critical to preventing these future breaches.”
Why This Makes Quantum Security Urgent Today
The harvest now, decrypt later, changes the timeline for action. Organizations do not have until quantum computers arrive. They have until adversaries finish collecting data that will still be sensitive when quantum computers become available.
If your data needs to remain confidential past 2035, it is already at risk. Encryption applied today using RSA or elliptic curve cryptography will not last that long once quantum computers capable of running Shor’s algorithm exist. The confidentiality window is closing, and the clock started years ago.
Cryptographic migrations take years to complete. Identifying where encryption is used, testing new algorithms, coordinating vendor support, and deploying replacements across complex infrastructure all require time. Organizations that wait until quantum computers are imminent will find themselves trying to secure data that adversaries have already collected.
The mismatch between how long data must stay secret and how long encryption can protect it creates the vulnerability. Encrypted communications from 2020 may need to remain confidential until 2040 or beyond. But if quantum computers capable of breaking that encryption arrive in 2032, the encryption fails eight years too early.
This is why migration to post-quantum cryptography is a present-day requirement for anyone protecting information with long confidentiality horizons.
What Makes This Threat Different
Traditional breaches are visible. Systems are compromised, alerts trigger, and teams respond within days or weeks.
“Harvest now, decrypt later” (HNDL) attacks work differently. Data is collected while still encrypted, with no immediate signs of compromise. The impact is delayed. Data that appears secure today can become readable years later as decryption capabilities improve. By that point, organizations may have no record of when or how the data was intercepted.
This delay complicates response and accountability. Attribution becomes difficult, evidence may no longer exist, and the systems involved may have changed.The risk is not immediate disruption, but the long-term exposure of sensitive information that was assumed to be secure.
Current Estimates on Timing
Experts disagree on exactly when quantum computers will pose a practical threat to widely used encryption. Estimates vary depending on assumptions about hardware progress, error correction advances, and algorithmic improvements.
Some projections place the threat as early as 2030. Others suggest 2035 or later. The range reflects genuine uncertainty about how quickly fault-tolerant quantum systems will scale.
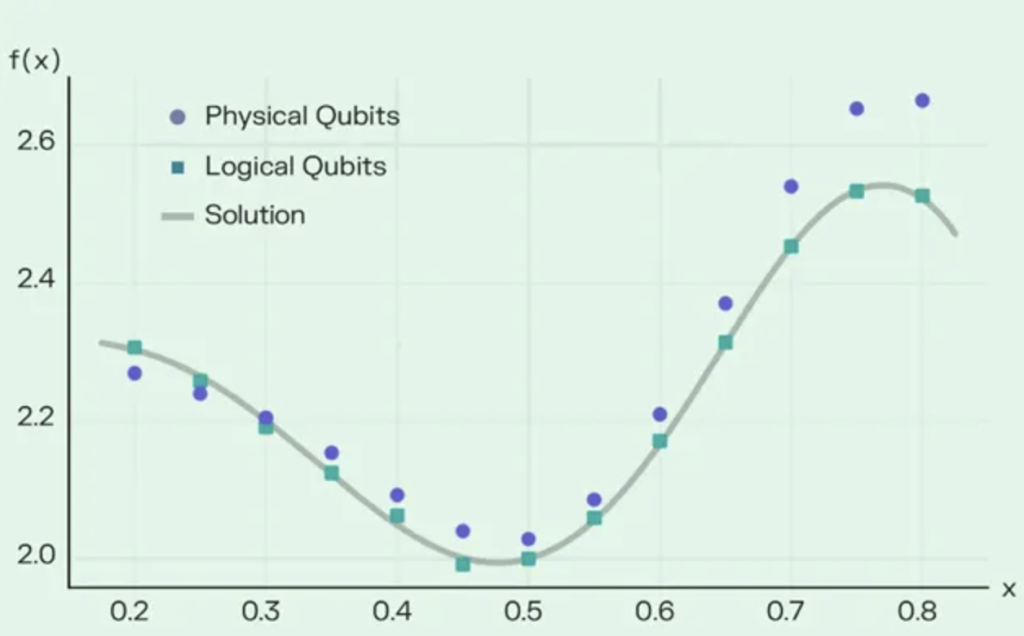
Recent research has compressed these timelines significantly. Three papers published between May 2025 and March 2026 reduced the estimated quantum resources needed to break RSA-2048 encryption from 20 million qubits to fewer than one million, and potentially as low as 100,000 qubits using newer architectures. What once seemed like a distant threat now appears closer than previously estimated.
But for organizations making decisions today, the precise timing matters less than the direction. Many projections from researchers, government agencies, and industry analysts suggest that quantum computers capable of breaking RSA-2048 and elliptic curve cryptography could exist within the next 10 to 15 years.
Given that cryptographic transitions take 5 to 10 years to complete, and that adversaries are already collecting data, the window for orderly migration is narrowing. Organizations protecting data that must remain confidential into the 2030s or beyond cannot afford to wait for more precise timelines. By the time the threat becomes certain, the data will already be in adversaries’ hands.
Who is Harvesting Data
State-level actors with intelligence capabilities represent the most significant threat. The NSA is known to operate infrastructure designed to collect and store massive volumes of data. Similar capabilities exist in China, Russia, and other nations with advanced signals intelligence programs.
A National Endowment for Democracy report specifically identifies China’s HNDL strategy as a major concern, noting that China has dedicated substantial resources to quantum research and is building quantum communication networks that could facilitate both secure communications and future decryption capabilities.
These organizations have the resources to intercept traffic at scale, the storage capacity to archive it indefinitely, and the institutional patience to wait years or decades for quantum computers to mature.
Sophisticated cybercriminal organizations may also engage in selective harvesting, particularly targeting financial institutions, healthcare providers, or corporations with valuable intellectual property. While criminals typically focus on immediate monetization, high-value targets with long-lived data could justify the investment in storage and patience.
Corporate espionage operations, whether state-sponsored or commercially motivated, may collect encrypted R&D communications or proprietary research. The data may remain dormant for years, but the competitive intelligence it provides once decrypted could still be actionable.
What Organizations Can Do Now
The most effective defense against harvest now, decrypt later attacks is migration to post-quantum cryptography. Data encrypted with NIST-standardized algorithms like ML-KEM, ML-DSA, and SLH-DSA is designed to resist attacks from both classical and quantum computers.
Organizations should prioritize systems protecting long-lived sensitive data. Government communications, healthcare records, financial transactions, legal files, and research data all fall into this category. These systems should migrate to post-quantum cryptography ahead of less sensitive infrastructure.
As detailed in previous Quantum Insider reporting, the “harvest now, decrypt later” threat creates urgency even though large-scale quantum computers do not yet exist. Data encrypted today using RSA or ECC may remain sensitive for years or decades, and adversaries do not need to wait for quantum computers to begin collecting encrypted data.
Hybrid cryptography provides a transitional approach. Combining classical encryption (RSA or ECC) with post-quantum algorithms ensures that data remains protected even if one system is compromised. An adversary would need to break both layers to decrypt the data.
Perfect forward secrecy limits exposure by ensuring that even if long-term encryption keys are compromised, past communications remain secure. Protocols that generate session-specific keys and delete them after use reduce the window of vulnerability. This does not prevent “Harvest now, decrypt later” attacks entirely, but it narrows the scope of what can be decrypted.
Data retention policies should be reevaluated. Information that does not need to be kept should be deleted. Encrypted data that no longer serves a purpose should not remain in storage where it could be intercepted. Reducing the volume of long-lived encrypted data reduces the attack surface.
Organizations should also be aware that vendor timelines matter. Cloud providers, software vendors, and hardware manufacturers all have their own post-quantum migration schedules. Systems that depend on third-party cryptography will only become quantum-resistant when those vendors complete their own transitions. Understanding vendor roadmaps is part of managing the “Harvest now, decrypt later” risk.
A Silent Threat Already in Motion
Every encrypted communication transmitted today using RSA or elliptic curve cryptography is vulnerable to this threat if it needs to remain confidential into the 2030s or beyond. Organizations protecting data with long confidentiality requirements face a closing window. The data is already being collected and the encryption protecting it will not last forever due to which migration to post-quantum cryptography is the only defense that addresses the root vulnerability.
Partner with the Year of Quantum Security 2026
This article is part of The Year of Quantum Security 2026 – a year-long editorial and convening initiative produced by The Quantum Insider, covering post-quantum readiness, quantum resilience, and responsible adoption.
Organizations supporting YQS2026 – post-quantum vendors, cybersecurity providers, telcos, and critical infrastructure operators – gain year-long editorial visibility across TQI, direct access to CISOs and policymakers, and category-leadership positioning at a pivotal moment in the security transition.
Founding Partner, Global Strategic, Program Partner, and Supporting Partner tiers are open for 2026.
→ Book a 20-minute briefing with Luke Preskey, CRO
QuantumSecurity2026.org | #YQS2026








![Origin Quantum, a Chinese firm quantum computing company, unveils its fourth-generation domestically developed superconducting quantum computer, Origin Wukong-180, on Saturday. [Photo provided to chinadaily.com.cn]](https://thequantuminsider.com/wp-content/uploads/2026/05/2026-05-15_19-58.png)
