Insider Brief
- Cloudflare has accelerated its timeline to achieve full post-quantum security by 2029, citing new research and industry signals that suggest quantum threats may arrive sooner than previously expected.
- Recent advances in quantum algorithms, hardware approaches such as neutral atoms, and improved error correction have reduced the estimated resources needed to break widely used encryption systems.
- The company is shifting focus from protecting stored data to securing authentication systems, warning that quantum-enabled attacks could allow adversaries to impersonate users and gain direct access to critical infrastructure.
Cloudflare is accelerating its timeline to secure the Internet against quantum attacks, citing new research and industry signals that suggest the threat may arrive sooner than expected.
The company said in a recent blog post that it is now targeting 2029 to achieve full post-quantum security across its services, including both encryption and authentication. The company writes the efforts are driven by recent advances in quantum computing that could undermine today’s cryptographic systems.
The move reflects a broader change in how the industry is assessing risk. For years, most efforts focused on protecting stored data from future decryption. Now, companies are increasingly concerned about real-time attacks that could allow adversaries to impersonate systems or gain unauthorized access.

Cloudflare pointed to two recent developments that appear to have pulled forward expectations for so-called “Q-Day,” the point at which quantum computers can break widely used encryption systems.
One came from Google, which announced it had significantly improved an algorithm capable of breaking elliptic curve cryptography, a method used across the Internet to secure communications. While Google did not disclose the algorithm itself, it provided a proof that it exists.
Another came from startup Oratomic, which published estimates suggesting that breaking widely used encryption standards such as RSA-2048 and P-256 may require far fewer quantum resources than previously believed. According to the analysis, a neutral atom quantum computer could potentially crack P-256 using around 10,000 qubits — a figure that surprised many in the field.
These developments suggest that the gap between current quantum systems and those capable of breaking encryption may be narrowing more quickly than expected, according to the post written by
Bas Westerbaan, cryptographer and Principal Research Engineer, Cloudflare. Westerbaan added these signals, along with broader industry momentum, prompted it to accelerate its own roadmap.
The company also indicated that some experts are now considering scenarios where high-value targets could face early, targeted quantum attacks before large-scale systems become widely available.
Three Fronts of Progress Converge
Cloudflare attributed the faster timeline to simultaneous advances across three areas: hardware, error correction, and software.
On the hardware side, multiple competing approaches — including superconducting qubits, neutral atoms, trapped ions, and photonics — have all made measurable progress in recent years. While no system has yet demonstrated the ability to scale to the levels required for breaking encryption, the company said each approach is closer than it was just a few years ago.
Error correction, which allows quantum computers to operate reliably despite noise, has also improved. Traditional systems may require hundreds or thousands of physical qubits to create a single stable “logical” qubit. New architectures, particularly those using reconfigurable qubits such as neutral atoms, may reduce that overhead significantly.
Software advances are compounding these gains. Improvements to quantum algorithms, including those targeting cryptographic systems, are reducing the computational effort required to break encryption.
Cloudflare said the interaction of these three areas makes predicting timelines difficult, as progress in one domain can amplify gains in others. The result is a scenario where incremental advances can quickly add up to meaningful capability.
From Encryption to Authentication
The company’s updated roadmap also reflects a shift in priorities.
Until recently, much of the industry’s focus was on preventing “harvest now, decrypt later” attacks, in which adversaries collect encrypted data today with the expectation of decrypting it once quantum computers become available.
Cloudflare said it has largely addressed this risk by enabling post-quantum encryption across most of its products. According to the company, more than 65% of human traffic passing through its network is already protected using post-quantum methods.
However, the company now argues that authentication — verifying identities and access credentials — presents a more immediate and severe risk.
If quantum computers can forge digital signatures or impersonate trusted systems, attackers could bypass security entirely. Unlike data decryption, which exposes past information, compromised authentication could allow real-time control over systems, including software updates, network access, and critical infrastructure.
Cloudflare described this scenario as potentially catastrophic, noting that a single compromised credential could grant persistent access until detected and revoked.
High-value Targets Likely First
The company said early quantum attacks, if they occur, are likely to focus on high-value targets rather than broad disruption.
These could include long-lived cryptographic keys such as root certificates, API credentials, and code-signing keys, which are assets that provide durable access to systems or large amounts of data.
Because early quantum systems are expected to be expensive and limited in availability, attackers would likely prioritize targets that offer the greatest return. Over time, as quantum hardware becomes more scalable, the threat could expand to broader classes of systems.
Cloudflare also warned that many organizations underestimate the complexity of upgrading authentication systems. Unlike encryption, which can often be updated centrally, authentication involves a web of dependencies, including third-party vendors, legacy systems and user devices.
The company said migrating to post-quantum authentication could take years, particularly in large or federated systems such as the web.
Compressed Roadmap
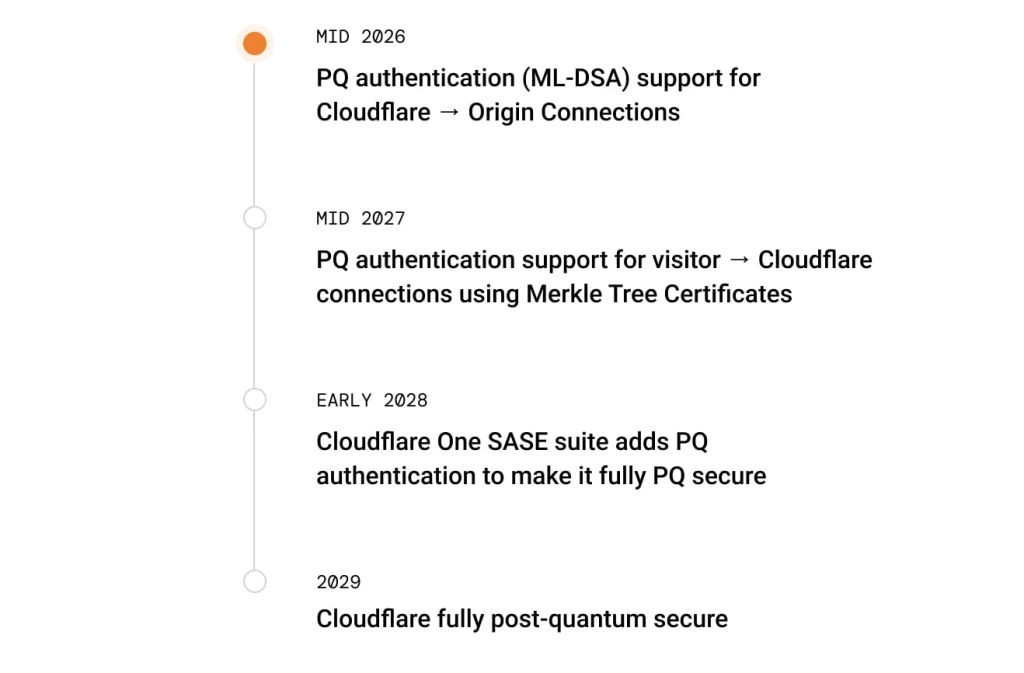
Cloudflare outlined a staged plan to reach full post-quantum security by 2029.
The company expects to introduce post-quantum authentication for connections between its network and origin servers by mid-2026. By 2027, it plans to extend this capability to connections between users and its network. Additional products, including its enterprise networking suite, are scheduled to follow by 2028.
The final milestone — full post-quantum security across all services — is targeted for 2029.
Cloudflare said it will continue to deploy these upgrades by default, without requiring customers to opt in, as part of its broader strategy to make security standard across the Internet.
Industry-wide Implications
Beyond its own roadmap, Cloudflare urged businesses and governments to accelerate their own preparations.
For companies, the recommendations include requiring post-quantum support in procurement decisions, assessing the readiness of vendors, and prioritizing upgrades for critical systems and long-lived credentials.
For governments, the company emphasized the importance of coordination and clear timelines to avoid fragmentation in standards and deployment.
Cloudflare said the question is no longer whether quantum computers will eventually threaten existing cryptography, but how quickly organizations must act to mitigate that risk.
“When experts in the field of building quantum computers start patching authentication systems, we should all listen,” Westerbaan writes. “The question is no longer ‘when will our encrypted data be at risk?’ but ‘how long before an attacker walks in the front door with a quantum-forged key?'”