Insider Brief
- IBM researchers are working with messaging platforms including Signal and Threema to explore how quantum-safe cryptographic techniques could be integrated into secure messaging systems.
- Researchers examined how Signal’s private group messaging protocol could be redesigned using post-quantum cryptography while maintaining privacy protections and reducing potential bandwidth increases.
- The work involves modifying the NIST-standardized algorithm ML-DSA and exploring integration of ML-KEM for messaging encryption, with findings presented at the Real-World Crypto Conference.
- Image by IBM.
Millions of people worldwide rely on messaging services to communicate with family, friends, and businesses. As mobile technology expanded, messaging applications became a central tool for modern communication.
Among secure messaging platforms, Signal has grown into one of the most widely used encrypted messaging services since its launch in 2014. The platform provides end-to-end encryption for messages, group chats, and video calls, meaning the encryption keys used to unlock conversations are generated and stored on users’ devices rather than on Signal’s servers.
IBM explains that breaking this type of encryption using classical computing would require an impractical amount of time. However, the company notes that advances in quantum computing could eventually affect how encryption systems operate.

Quantum Computing and Encryption Research
Quantum computing has progressed from theoretical physics to engineering over the past several decades. Unlike classical computers, which process information using bits representing either 0 or 1, quantum computers use qubits. These qubits can represent combinations of states through superposition and can be linked through entanglement, enabling quantum systems to explore many computational possibilities simultaneously.
These properties could allow quantum computers to solve certain problems faster than classical machines, including mathematical operations used in modern encryption systems.
As quantum computing advances, researchers have worked to develop new cryptographic approaches designed to resist attacks from future quantum systems. In 2024, the National Institute of Standards and Technology (NIST) released its first three post-quantum cryptography standards. Two of those algorithms were developed by IBM Research scientists, while a third was co-developed by a researcher who later joined IBM Research.
Developing Quantum-Safe Messaging Protocols
IBM reports that while these standards provide a foundation for quantum-safe security, some applications require more advanced cryptographic methods. In some cases, quantum-safe alternatives may be less efficient than existing cryptographic schemes.
“Nobody wants to use more cryptography than they really need,” said Vadim Lyubashevsky, principal research scientist at IBM Research working on quantum-safe cryptography.
These limitations led researchers to examine how existing systems could evolve beyond the initial standards. Through collaboration with Signal’s development team, IBM researchers began exploring how group messaging on the platform could be made quantum safe.
Redesigning Private Group Messaging
Signal’s security design minimizes the information the service collects about users. This includes limiting metadata about who sends messages and who joins or leaves groups, while maintaining controls that prevent unauthorized access.
Organizations face a risk known as “harvest now, decrypt later,” in which attackers collect encrypted data and store it until future technologies enable decryption. Signal has implemented measures since 2023 to protect user data against such attacks and introduced a protocol upgrade known as SPQR in 2025 to strengthen those defenses.
When researchers examined how Signal’s existing private group protocol could be adapted for quantum-safe cryptography, they found that replacing current components directly could significantly increase network bandwidth usage which can potentially lead to up to a hundredfold increase in bandwidth requirements, source reported.
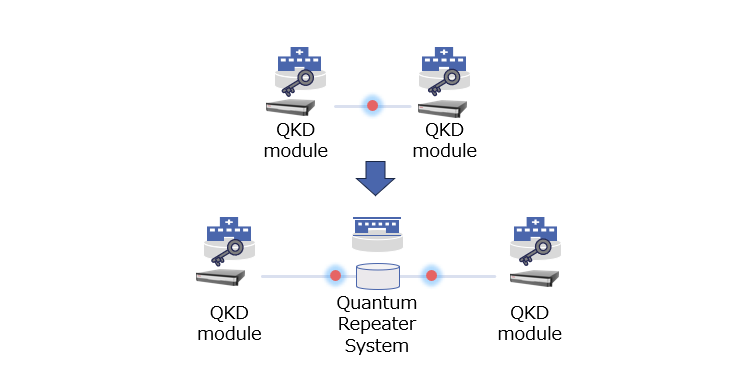
To address this issue, researchers proposed redesigning the protocol. Instead of relying solely on Signal’s server to manage group membership, the proposed design allows group members to act as part of the verification process.
Under the approach described by IBM, servers would store encrypted group data and enforce message-writing permissions. Each member would receive a pseudonym key for group activity, allowing the server to track actions associated with group positions without linking them to real identities.
Cryptographic Techniques and Research Development
To support this design, researchers modified ML‑DSA – a lattice-based digital signature algorithm standardized by NIST – to enable key re-randomization.
The team also developed a new security model that accounts for different user roles within groups and possible compromises of servers or group members.
IBM said the redesigned approach was developed in collaboration with Signal engineers and aims to maintain the platform’s privacy guarantees while improving efficiency and modularity.
The research team is presenting the work at the Real‑World Crypto Conference, and Signal plans to explore potential implementation approaches, IBM reported.
Threema Collaboration on Quantum-Safe Messaging
Another secure messaging service, Threema, has also begun exploring quantum-safe cryptography.
Threema is working with the same research team to evaluate how ML‑KEM – another NIST-standardized algorithm developed by IBM researchers, can be integrated into its messaging system.
“The scientists at IBM have incredible expertise in quantum-safe cryptography,” Threema CEO Robin Simon said in remarks cited by IBM. “This collaboration and the pooling of our expertise lay the foundation for the quantum-secure communication of tomorrow.”