Security protocols and systems developed to protect from future quantum computers are part of a market called quantum security. With algorithms like Shor’s algorithm, quantum computers could compromise traditional cryptographic methods, which rely on mathematical problems that are hard to solve for traditional computers.
There is growing concern about quantum computing’s potential threat to existing data protection systems as it advances. To combat this, researchers and experts are developing new cryptographic techniques that can withstand quantum computer attacks to address this issue.
What is Quantum Security and how does it Work?
Quantum security (also known as quantum cryptography) is a cybersecurity branch dedicated to safeguarding sensitive information from the potential risks posed by future quantum computers. Some complex mathematical problems could be solved much faster by quantum computers, which could make many traditional cryptographic algorithms vulnerable. Such algorithms include Rivest–Shamir–Adleman (RSA) and Elliptic Curve Cryptography (ECC). A key difference between RSA and ECC is that the former relies on the difficulty of factoring large numbers, while the latter relies on the difficulty of solving discrete logarithms on elliptic curves. It is expected to be possible to solve these problems on a large-scale quantum computer running Shor’s algorithm, posing a significant security threat to these systems.
The goal of post-quantum cryptography is to design cryptographic algorithms that are resistant to quantum computer attacks. This is not to be confused with QKD which allows partners to securely exchange encryption keys. The security of QKD is ensured by the fundamental principles of quantum mechanics and requires specific hardware/tech to implement. PQC (post-quantum cryptography), on the other hand, is a type of cryptographic algorithm (usually a public-key algorithm) that is thought to be secure against a cryptanalytic attack by a quantum computer.

The Nature paper, Transitioning organizations to post-quantum cryptography, published in 2022, presents an organizational perspective of the PQC transition and is recommended reading.
Quantum Security vs. Traditional Data Transfer Security
Quantum security uses quantum mechanical principles to provide fundamentally secure data transfer security instead of traditional computational complexity assumptions and offers a stronger defense against attacks. Quantum security protocols, however, are still in the early development stages and have not yet been widely deployed. Even though traditional security methods continue to play a critical role in securing data transfer, their viability in the era of quantum computing remains uncertain.
What is Quantum Key Distribution (QKD)?
In quantum key distribution (QKD), cryptographic keys are distributed securely between two parties, usually referred to as Alice and Bob for explanatory purposes. To ensure the tamper-proof exchange of keys, it utilizes quantum mechanics principles such as quantum entanglement and the no-cloning theorem. QKD can detect eavesdropping attempts by encoding information in quantum states, such as photon polarization. If quantum bits are interfered with, Alice and Bob will be able to detect these errors and thus create a secure key. By using QKD, secret keys that are resistant to interception can be generated. One company incorporating Quantum Key Distribution into its operations is Quside.
Quantum Resistant Encryption (Post-quantum Encryption)
A quantum-resistant encryption algorithm, also known as post-quantum encryption, is a cryptographic algorithm designed to resist future quantum computer attacks. A post-quantum encryption algorithm relies on mathematical problems that are believed to be difficult for both classical and quantum computers to solve. There are many different types of post-quantum encryption algorithms, such as lattice-based cryptography, code-based cryptography, multivariate polynomial cryptography, and hash-based cryptography. Even if an adversary has access to a large-scale quantum computer in the future, these algorithms aim to ensure security.
Post-quantum encryption standards are being developed and adopted continuously. Standardization bodies in the United States, such as NIST, are evaluating several algorithms at present. As we move into the world of quantum computing, NIST and other government agencies around the globe are working tirelessly to identify an appropriate set of post-quantum encryption algorithms that can replace existing cryptographic standards and ensure long-term security.
Despite its growing awareness amongst security professionals, post-quantum encryption is not yet widely used in practice due to the complexity of transitioning from traditional to quantum-resistant cryptographic algorithms. Nevertheless, organizations should examine their cryptographic systems and develop strategies for transitioning to quantum-resistant encryption when the time comes in preparation for the post-quantum era. In the future of quantum computing, advancements in quantum control may revolutionize data transfer security by leveraging the principles of quantum manipulation.
Implementing Quantum Security Against Cryptographic Attacks
There are several practical implementations that could possibly combat future cryptographic attacks, one of which is quantum key distribution (QKD), which enables the secure exchange of cryptographic keys between parties, mentioned above. As another application, quantum-resistant cryptography focuses on developing algorithms that are resistant to attack by quantum computers. As cyber threats become more sophisticated, quantum security holds promise for safeguarding sensitive information.
Challenges and Limitations in Implementing Quantum Security
Due to the unique properties of quantum systems, quantum security poses several challenges and limitations. To begin, let’s take a look at some challenges and limitations:
- The complexity of technology currently requires specialized expertise for its development, deployment, and maintenance.
- The scaling up of quantum security systems is another significant challenge. Quantum key distribution (QKD) protocols require specialized hardware and infrastructure. Quantum communication becomes increasingly challenging as the number of users and the distance between them increase.
- Owing to the intrinsic properties of quantum states, QKD systems have a limited range, because the transmission of quantum information can easily result in small particles such as photons being absorbed, scattered, or lost. It is therefore currently necessary to use trusted nodes or repeaters to extend the range of secure quantum communication.
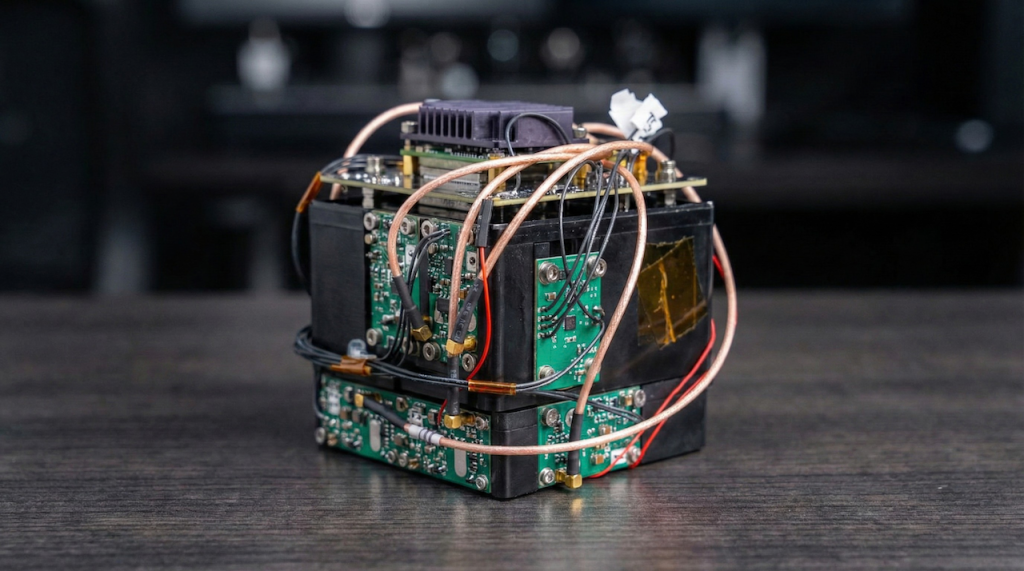
- Another barrier to universal adoption of the technology is the cost of quantum security technologies and their accessibility to the general public, which are currently prohibitive or seen as an unnecessary expense for some organizations. A quantum key distribution device, a quantum random number generator, or a quantum-resistant cryptographic solution can cost multiple thousands of dollars.
- Finally, for widespread adoption, interoperability and standardization across different quantum security systems and protocols are essential. Despite this, achieving universal standards and compatibility remains a challenge due to the diversity of quantum technologies and ongoing research and development.
While these challenges and limitations persist, ongoing research in quantum security is aimed at addressing these issues and paving the way for the practical implementation of quantum-safe cryptographic solutions and secure quantum communication networks.
You may also like:
What is Quantum Computing? [Everything You Need to Know]
5 Crucial Quantum Computing Applications & Examples
What Are The Remaining Challenges of Quantum Computing?
Will Quantum Computing Pose a Security Threat?
A growing number of researchers and cryptographers are working on developing quantum-resistant algorithms that are resistant to attacks by quantum computers. Even in the presence of quantum technology, these algorithms are designed to withstand the computational power of both classical and quantum computers.
Jack Hidary, CEO of SandboxAQ, highlighted in an interview at the Economist Impact event in London in 2022, the fact industry needs to transition from RSA (Rivest-Shamir-Adleman), an asymmetric encryption technique that uses two different keys as public and private keys to perform the encryption and decryption, to post-RSA, and realized that after decades of using it, it’s time to store-now, decrypt later, known by its acronym as SNDL.
It is important to note that despite the potential security threats that quantum computing poses to current cryptographic systems, quantum-resistant algorithms are being developed to address these concerns in the face of the challenges of quantum computing. Governments and organizations should monitor quantum computing’s progress and be prepared for its potential security implications.
To find out more about quantum security and the threats it could have for society, please check out the 2023 Quantum Security Report from The Quantum Insider, which offers readers a deep understanding of the quantum security market size and key players in the growing quantum security ecosystem that seeks solutions to security and privacy in what experts refer to as the post-quantum cryptography era.
Featured image: Image by Pete Linforth from Pixabay
If you found this article to be informative, you can explore more current quantum news here, exclusives, interviews, and podcasts.