Awareness. Agility. Action.
It’s a three-step process that Quantropi’s chief technology officer and long-time technology leader sets out as an important – if not existential – plan for organizations to prepare for the moment when quantum computers can crack cryptographic schemes that currently protect data and communication, a seismic cybersecurity shift.
“It has to start with education,” said Michael Redding, Quantropi CTO. “That’s the first step: get aware. And you don’t have to become a cryptographer. You don’t have to become a quantum mathematician. But just understand that this is really happening.”
Redding is a passionate advocate for immediately confronting what experts are now referring to as Y2Q, a nod to the tech upheaval of Y2K. In 2000, companies faced potentially catastrophic errors because of the reliance on a two-digit annual calendar. Programmers in the 1970s and 1980s thought using a two-digit calendar would save valuable space and memory, but fears about the problems these calendaring errors might create, once ignored, began to grow to a fever pitch in the late 1990s.
“In Y2K, there was this one little coding decision in two bytes instead of four that put all computer systems at risk of going slightly haywire, which goes back to those COBOL days because you didn’t have a lot of bytes, so you shaved off two,” said Redding. “No one looked that far, nobody looked 20 years down the road. So, Y2Q is the same story over again.”
However, Y2Q may be much more difficult to manage for a few reasons, he added. First, Redding said Y2K had a definite start date – Jan. 1, 2000. The deadline gave companies a precise moment to rally around and time to prepare for the event, which, ultimately, did not end in the forecasted disaster. Y2Q might not be so forgiving. The precise timing of when quantum computers can hack current cryptographic schemes is still uncertain, he pointed out.
“That’s the big question – When is this going to happen – and the answer is, it depends on who you ask,” said Redding. “Some people say this will happen 12 to 18 months. A company could bring a 1 million qubit processor online commercially next year and people have guessed that about a million qubits might be enough to run Shor’s algorithm. On the other hand, experts wonder if a million qubits would be sufficient only if they have the right kinds of qubits. And then there are others who say it’s farther away, 20 years out, and, of course, others are guessing somewhere in between next year and 20 years.”
The uncertainty baked into that debate might still give tech leaders wiggle room to procrastinate, but Redding said companies must still grapple with the “steal now, decrypt later” potential of quantum computer-powered hackers. Redding said that hackers could collect data – even though that information is safely encrypted with classical cybersecurity algorithms – and simply wait until quantum computers come on line. Then, they could decrypt it with this powerful new quantum technology. The result would be a treasure trove of data.
“There is all this data sitting out there right now in cloud storage, just waiting for a quantum computer and AI that can read it all,” said Redding. “And, when that happens, all of it will be vulnerable. Of course, maybe 99.9% of these pieces of information are going to be pictures of my dog, or pictures of when I’m having dinner. But, some percent of this data could include stealth bomber plans, or embarrassing photographs of a Senator – which still are going to have value five or 10 years from now.”
In other words, while most companies are asking themselves when the quantum threat will arise, Redding said that’s the wrong question. The quantum threat is now.
“The threat is imminent, but the risk is actually already persisting – and that’s a real problem,” said Redding.
Agility
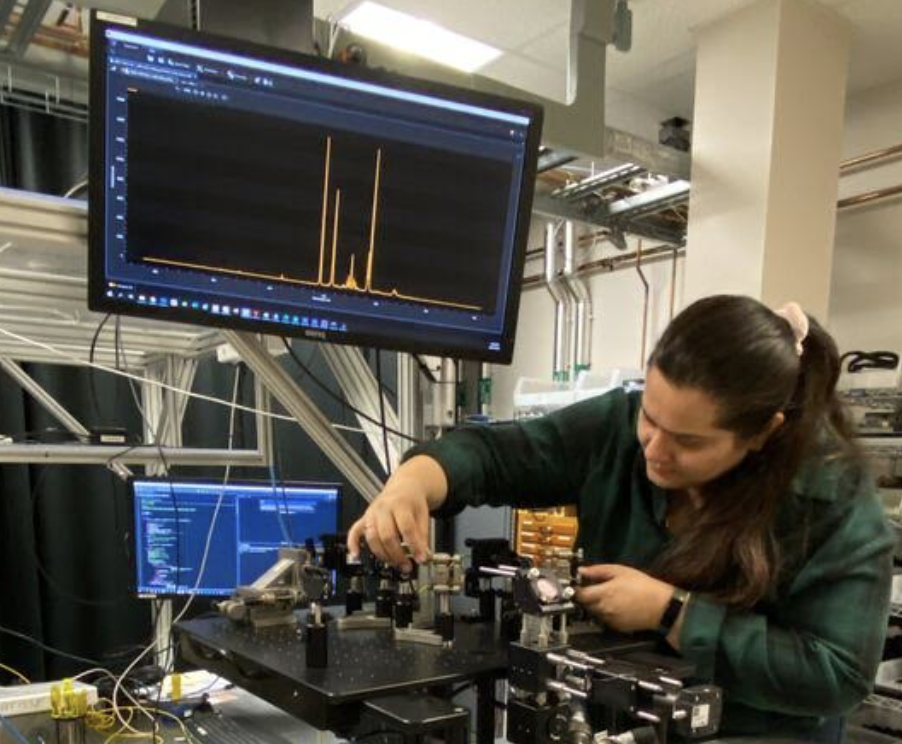
To face down this threat, organizations need the right tools and weapons. Redding said Quantropi is developing not just a tool, but several tools, that create a Software as a Service (SaaS) platform for – what he terms – crypto agility.
Quantropi has created this platform of solutions – called QiSpace™ – to attack possible approaches to quantum hacks in multiple ways and remain crypto-agile in the future. They call this suite “TrUE” – which stands for Trust, Uncertainty and Entropy.
The technologies establish Trust between parties with a quantum-secure asymmetric MASQ™ encryption. QEEP™ uses Uncertainty, specifically symmetric encryption, to defend against attacks and provides Quantum Entropy Services with SEQUR™ to develop ultra-random key generation and digital distribution to enable secure data communications – a type of Digital QKD.
Crypto agility gives the user the ability to not just protect against the current understanding of quantum threats, but better position their organization to meet future attacks and update the system with state-of-the-art cryptographic algorithms, said Redding. Referring to the National Institute of Standards and Technology’s sanctioning of its first group of post-quantum cryptographic algorithms, Redding said that Quantropi’s platform could easily adapt to these – as well as new PQC algorithms.
“In the spirit of crypto agility, as NIST finalizes certain standards and ratifies those as Internet standards, we’ll make that part of our platform too, because we want the customer always to be able to pick and choose the right tool for the job,” said Redding.
Action
Because it is no longer a question of if quantum computers will crack today’s cybersecurity measures, but when – and because hackers have the ability to steal data now and decrypt the information later – Redding said organizations must get serious about post-quantum cryptography and they must get ready now.
“This is really a wake-up call to take action,” said Redding. “I don’t care whether you end up using our solutions – I hope you do – but the most important thing for you to do is to become aware of the problem and the solutions.”
On the organizational level, that awareness should be followed with action, even a quick assessment of possible vulnerabilities can help put the organization on the right post-quantum path.
“Get aware and maybe even start to conduct, just a preliminary – a quick and dirty – inventory of your systems,” said Redding. “If you’re a good IT shop, you probably have a good idea, but you can ask yourself the questions: Which applications or what datasets are vulnerable? Or what network transmission? Think about: ‘What’s something that, if it would be compromised, would be really bad?’ Those are some of the initial questions that can guide decision makers on what to do next.”
Vision and Mission
If it sounds like Redding thinks he is on a world-saving mission to mitigate what might be the biggest technological threats of the past two decades – at least – it’s because he is. In fact, Redding came out of retirement due largely to his concern about the post-quantum era in tech and Quantropi’s vision matched his own for handling the issue.
After a long career at Accenture where Redding headed up the company’s research and development wing for several years, overseeing several laboratories, including a Washington D.C.-based cybersecurity lab. His last duty was as a co-founder and lead of Accenture Ventures, a position he held for five years until retirement. Accenture Ventures invested in a range of cutting-edge technologies, including AI, blockchain and cybersecurity, as well as the early days of quantum.
During his career at Accenture he saw the disruptive power – both positive and negative. He saw first-hand the power of quantum’s positive potential, such as a Biogen and D-Wave collaboration that showed the promise of quantum computers to perform drug discovery.
A Quick Retirement
When the history of Quantropi is written, there will be an apocryphal tale about Redding flying to Canada in the winter – during a pandemic – to discuss coming out of retirement and becoming the company’s CTO. It’s a trip that can only be inspired by the awe of what the power of quantum can do in the right hands and a shared vision of ensuring the world is safe from people wielding quantum for the wrong reasons.
“I believe in the vision,” said Redding “We have a vision of preserving truth and trust, and preserving the way the world works against these current and future threats. That’s what got me to drop everything, hop on a plane in a winter in a pandemic, and, to come out of retirement – which didn’t last very long.”
You can go here for more information on Quantropi and navigate here for more information on QiSpace, the company’s SaaS platform for end-to-end quantum security.
If you found this article to be informative, you can explore more current quantum news here, exclusives, interviews, and podcasts.