Insider Brief
- A team of blockchain and quantum cryptological specialists are developing a framework to create quantum-safe blockchains.
- The team includes scientists from LACChain, Quantinuum and Tecnologico de Monterrey.
- They published their findings, which includes a five-step process to ensure maximum protection, in Scientific Reports.
A team of blockchain and quantum cryptological specialists are developing a framework to help protect blockchain networks from attacks by large and robust quantum computers, according to a blog post on the findings.
The team, which included scientists from LACChain, Quantinuum and Tecnologico de Monterrey, published their findings in Scientific Reports journal from Springer-Nature.
Quantum computers will present a significant challenge for blockchain, a decentralized, digital ledger that records transactions in a secure and immutable way.

According to the paper: “The advent of quantum computing threatens blockchain protocols and networks because they utilize non-quantum resistant cryptographic algorithms. When quantum computers become robust enough to run Shor’s algorithm on a large scale, the most used asymmetric algorithms, utilized for digital signatures and message encryption, such as RSA, (EC)DSA, and (EC)DH, will be no longer secure. Quantum computers will be able to break them within a short period of time”.
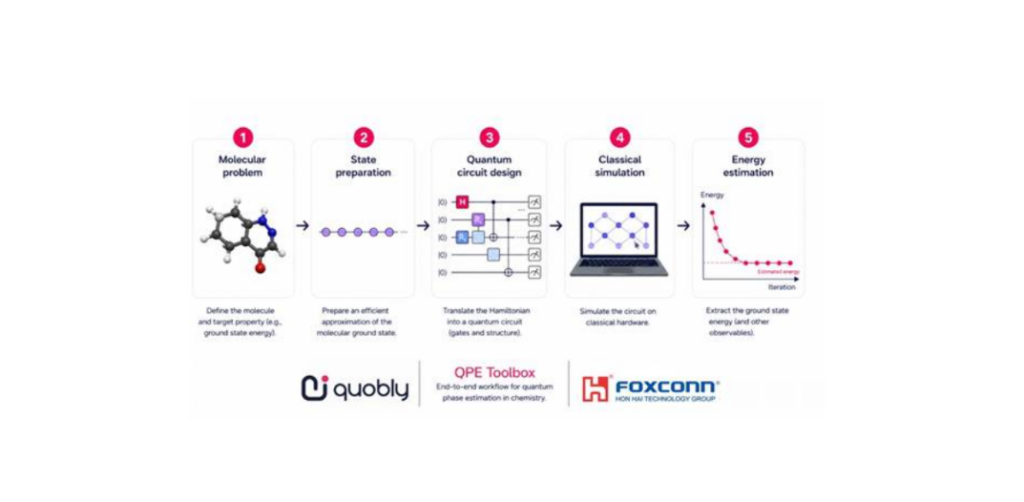
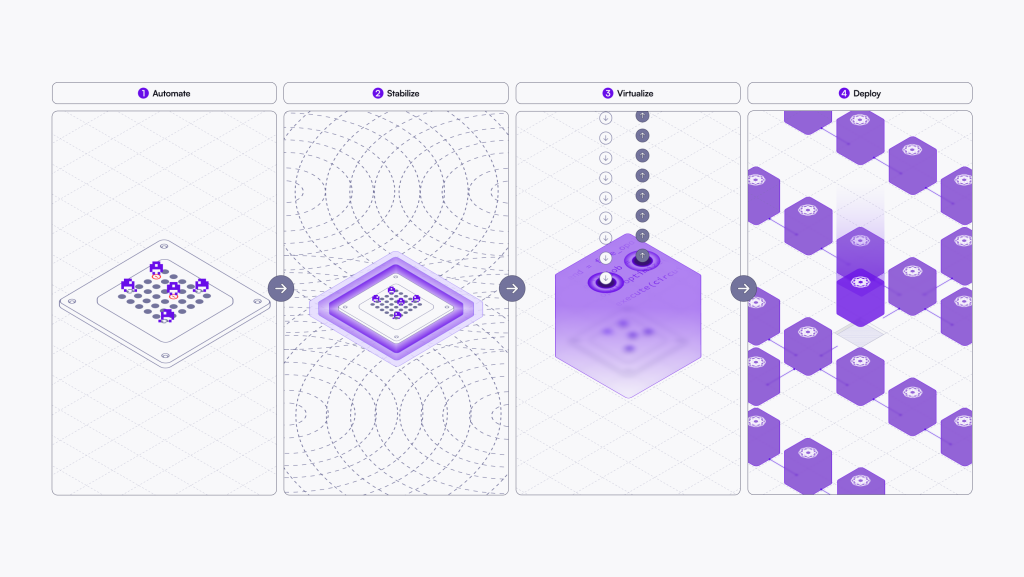
The team developed five-step end-to-end framework that could suit most blockchain networks and that won’t require critical modifications of the baseline protocols to add a post-quantum cryptographic layer for resisting quantum computer attacks. The joint team has also developed a scalable implementation for Ethereum-based networks which has been deployed in LACChain, that uses Hyperledger Besu as the blockchain protocol.
The steps include:
- Using Quantum Origin as a centralized entropy source. We also detail how the entropy is provided to every node using quantum-safe connections based on McEliece KEM keypair exchanges. Our use of quantum entropy is pioneer in the literature.
- Using quantum entropy in every node3 to generate Falcon keys and post-quantum X.509 certificates.
- Using nodes to leverage their post-quantum X.509 certificates with Falcon-512 public keys to establish quantum-resistant TLS tunnels.
- Using the nodes’ post-quantum Falcon-512 keys to sign every transaction they broadcast to the network.
Marcos Allende Lopez, CTO of LACChain and leader of this work said, “Today the blockchain community is focused on urgent needs such as scalability and interoperability. However, considering that there are trillions of dollars in value stored in blockchain networks and that according to Boston Consulting Group tokenization is expecting to become a $16 trillion market in 2030, it is irresponsible to not have a plan to protect decentralized ledgers from attacks by quantum computers that will be able to discover private keys and steal assets. Despite it is uncertain when large and robust quantum computers will be ready to accomplish that, it is very plausible that these machines are used silently at the beginning for hacking strategically without being spotted.”
The researchers also describe open-source development that offers three alternatives for the blockchain verification of transactions signed with the Falcon-512 NIST-compliant post-quantum signatures: implementing the verification code in Solidity which constitutes – to our knowledge – the first smart contract capable of verifying post-quantum signatures, implementing solidity instruction in the Solc compiler and corresponding EVM opcode, and refactoring the EVM opcode Java from the EVM virtual machine into a pre-compiled contract.
Professor Salvador E. Venegas-Andraca, of Tecnologico de Monterrey, commented: “Quantum technology is a give-and-take discipline: on the one hand, quantum computers together with Shor’s algorithm will eventually become a vulnerability to public key cryptography protocols and other technologies used in digital data protection. On the other hand, we can use quantum technology to increase the security of current and future data. The latter is indeed the core of our paper: to use quantum technology to protect current and future blockchains from quantum attacks.”.
Duncan Jones, Head of Cybersecurity at Quantinuum, added: “The most valuable digital assets demand the highest levels of security. By combining quantum-safe algorithms with quantum-computer-hardened keys from our Quantum Origin platform, this work demonstrates a significant security improvement for blockchain systems.”
The team is now looking to work with Ethereum and Hyperledger communities for further development of quantum-safe blockchain.
If you found this article to be informative, you can explore more current quantum news here, exclusives, interviews, and podcasts.