The natural acceleration of technological evolution provides humans with new opportunities, paving the way toward a future that seemed to be science fiction only a few years ago. That said, groundbreaking technologies that will be adopted down the road will give rise to equally revolutionary threats. These concerns require an all-new approach to security and collective solutions that should be implemented on a global scale.
The computation speed of quantum computers is multiple orders of magnitude higher than that of their classic counterparts. Not only does this save a ton of time when processing the most complex tasks, but it also calls forth new threats in areas like cryptography.
The progress of quantum technology could transform society and multiple industries. Businesses and governments should accurately assess the scale of the phenomenon along with the associated risks and start building quantum security. To unleash the full power of this promising tech, decision-makers need to address the distributed and systemic risks that require collective action and solutions.
The quantum arms race
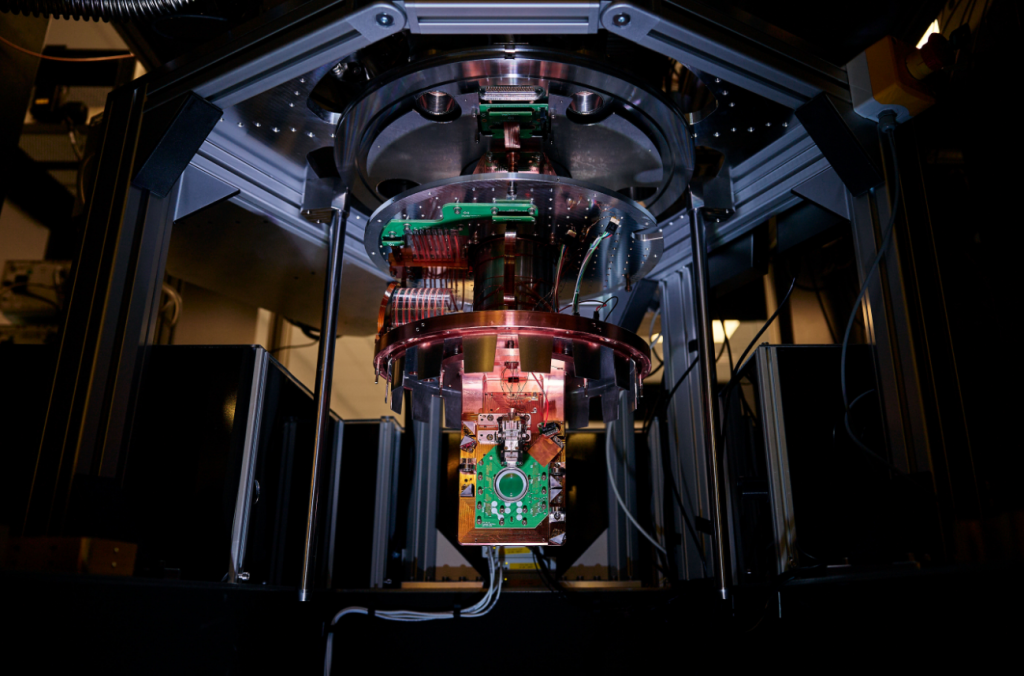
Quantum computing systems are capable of completing data processing tasks traditional computers cannot handle. In the next 5-15 years, such machines will underlie a strategically important technology potent enough to become a foundation for a new technological revolution.
Nowadays, researchers are solving complex engineering problems to create hardware and software that will allow the theoretical potential of quantum computing to be put into practice. Forecasts regarding the practical uses of the technology vary. It is generally believed that mankind will see the first real-world results within a decade.
However, these could be pessimistic predictions as significant funds from corporations and governments are being invested into the development process. The potential trillions of dollars in profits set a technological arms race in motion.
Quantum algorithms will be able to perform simulations at the molecular level, accelerating the discovery of new drugs and high-tech materials. The unprecedented computing speed will optimize the finance sector and the aerospace industry, opening new horizons for the potential of artificial intelligence (AI).
A small range of companies is already offering pilot versions of quantum computing services. These projects encourage customers to combine efforts with developers and create the algorithms required to fully implement the tech in a target sector.
The benefits are already attainable or will become attainable soon. The progress stemming from the evolution of quantum computers has not been fully converted to practical applications. But it is already clear that not only companies, but entire nation-states may fall behind the mind-boggling progress some will achieve.
Cryptographic risk – the least of all evils
The global cybersecurity community is already seeing the challenges associated with the quantum arms race. Here is a rundown on these roadblocks.
Violation of the cryptographic infrastructure. Quantum computers boast data processing speeds that pose a risk to asymmetric encryption, which currently underlies the security of numerous digital processes. Quantum-safe solutions are emerging that are not susceptible to this issue as they leverage post-quantum cryptography. Nevertheless, a number of implementation problems have yet to be addressed. The balance could be ruined if quantum computing becomes the privilege of a few individual members of the ecosystem. In this scenario, everyone else will be unable to ensure the confidentiality, integrity, and availability of their data.
Harvest now, decrypt later. This risk applies to data and systems that stay unaltered over time and inherently have a long service life, such as satellites and certain kinds of transport. Threat actors can collect data from these entities now and decrypt it in the future. They could also sell this information to interested parties who have already mastered quantum technology.
Geopolitical risks and equal access. The competitive advantages of quantum computing can deteriorate international relations, thus posing geopolitical risks. The accessibility of the technology to some countries and the “quantum poverty” of others may become serious obstacles to unlocking the potential of quantum computing.
New and secondary risks. These are related to the adoption of this technology in various sectors. For instance, malefactors may interfere with algorithms and leave backdoors when the technology is being implemented – this way, they will be able to control it later for their own benefit. Computational power can become the pivot of new cyber-attack vectors or be used to mastermind pathogens, viruses, bioweapons that may create disruptive economic advantages in the global markets.
Required security solutions
Quantum computing could have a jaw-dropping potential in the cybersecurity context. Although some players in this ecosystem have not added quantum risks to their security equation yet, the appropriate protection solutions are already taking shape.
However, companies and officials need to take more effort in this regard. Businesses will have to understand and properly evaluate risks related to quantum security. The most significant components of this process are as follows:
- Acknowledgment of quantum risks to the company’s infrastructure as well as an inventory of critical data assets.
- Professional management of the company’s encrypted data and a roadmap for switching to quantum-safe cryptography.
- Staying on top of the emerging vulnerabilities that can be exploited by attackers with quantum computing power at their disposal. Security controls that hinge on computing resources are particularly important.
- Understanding the dependencies on partners, suppliers, and B2B services.
- Realizing the benefits of embedding quantum computing into the company’s business model along with the potential risks of this shift.
Organizations should nurture the quantum literacy of their employees and senior management alike. This will play an important role in accurately assessing security risks and funding the quantum security department at a decent level.
Let us now go over some key quantum computing security issues and applicable solutions.
Distributed risk. Shared infrastructures and interdependent sectors of the ecosystem require collective action to ensure quantum security. In some cases, these initiatives will need to be coordinated among multiple parties.
Safe quantum development practices. Not only is this about educating qualified personnel with a profound understanding of the technology’s complexity, but it is also about permanently refining the knowledge and qualifications to properly evaluate the security risks at all tiers and fend off malware attacks.
Management principles. Standards and regulations are required to ascertain that companies assess risks in the quantum security arena. The same goes for decisions at the level of governments and regulatory authorities that should encourage companies to respond to the quantum threat adequately. International technical standards also need to be developed to eliminate barriers to further coordinated action. The ethical use of quantum computing is another growing issue that is escalating as the technology evolves. In this regard, the experience gained in international regulation of AI development could come in handy.
Equal access. To avoid a technology gap between countries and to balance the benefits of quantum computing across the board, governments will need to team up. Consensual equal access to the technology will release its full potential and provide maximum security for all participants in the ecosystem in the face of potential cyber threats of the quantum future.
Takeaways
Today’s global cybersecurity level is far from being perfect, but it suffices to maintain stability and avoid catastrophic consequences if failures happen. This may change in the near future, though. The development and implementation of quantum computing, artificial intelligence algorithms, and other sophisticated systems, as well as the growing complexity of network infrastructures and the interdependence of different sectors, will give rise to new systemic issues and risks. In such a paradigm, a security incident in one part of the system can impact the operation of another.
To steer clear of critical problems, all players in the dynamic cyberspace need to cooperate more tightly to reach a whole new level of security. The right time to start doing it is now. Not only do some technologies unearth information security issues of the future, but they also underlie ethical dilemmas that require careful discussion and regulation today.
For more market insights, check out our latest quantum computing news here.