Hypothesis Smashed
As technological innovations become more sophisticated — with talk of blockchain, 5G networks, Bitcoin and the Internet of Things (IoT) improving at a rate that smashes the Moore’s Law hypothesis into the oblivion of history, the threat becomes more apparent as to how, when the technology is fully-operational, how we will deal with the security issues that obviously arise.
We know we live in exciting times. But with the promise come the dangers. One area where this will be a salient point is with quantum computing and the technology that follows on from it.
A Few Years From Now

It is predicted quantum computers will have far-reaching effects on our lives, from in the military, medical research to how our urban centres are planned and designed.
‘On the one hand, this is incredibly exciting, as it will give us a huge amount of processing power that will revolutionise what computers are capable of. On the other hand, it will have massive — and potentially devastating — security repercussions for companies globally.’
— Thorsten Stremlau, Senior Engineering Staff Member and CTO within Lenovo’s Intelligent Devices Group PC & Smart Devices business
As quantum computers get better, they will have the potential to break current asymmetric encryption methods and algorithms, such as those based on RSA and elliptic curve cryptography. This will be a disaster for organised society which relies heavily upon these kinds of encryption modalities to keep our data secure.
If we don’t act now to protect ourselves the future won’t be bright.
Quantum Readiness
A new theory, first formulated by thought leaders at Thales eSecurity — a world-renowned company in data protection and a subsidiary of the Thales Group, a French multinational concern — is being bandied about by tech journalists, publications, academics and researchers. This theory, then, is called ‘crypto-agility’, otherwise known as ‘quantum readiness’.
Crypto-agility — is not a new fitness fad to help us shed the pounds — but rather a stance, a philosophy mind, if you will, to get us into the groove of technological preparedness for the coming storm that improvements in quantum computers will inevitably provide.
The potential power these computers have will be a threat to us all if we don’t take heed.
Group Effort
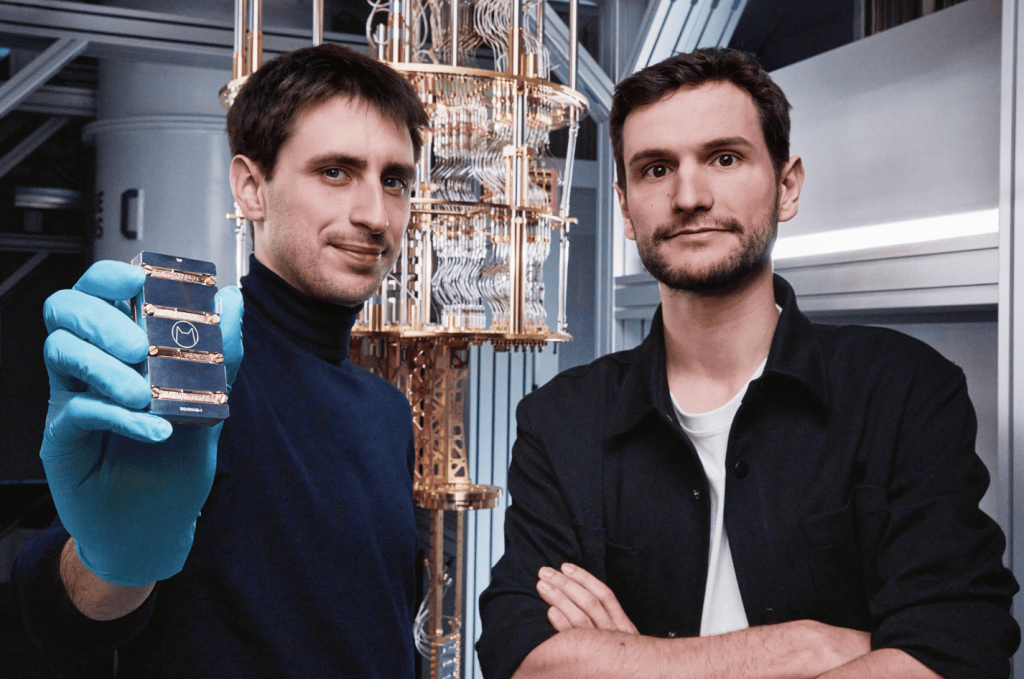
To get there, though — and make the technology work for us rather than against us — is going to take a group effort, a collaborative surge forward where not only scientists are involved, but business people, too.
We must learn how our data security issues will reshape in regard to the changes in quantum computing’s development. And how they must refashion with the improvements in the technology rather than lag behind.
It would be shooting oneself in the foot by just keeping the attitude of ‘seeing how things pan out’ in the world of quantum computers. Current encryption methods must be aligned with the innovation within the quantum computing space so that technological innovation in one can be matched by the other. That means crypto-agility will be sustained for our data protection, rendering quantum computers a non-threatening technology we can work with, rather than fight against.
While quantum computing is in its early stages, with minimum use cases of its successful implementation, security firms must watch closely as to any breakthroughs in the technology — as is the case with the ‘quantum advantage’ and ‘quantum supremacy’ hypotheses — and make sure their own infrastructure is good enough to cope with any possible infractions in cybersecurity.
At Thales eSecurity we are optimistic about the future
of post-quantum cryptography. Our products and
services are preparing for the necessary changes, while
the industry as a whole is on track to identify the safest
algorithms to use way ahead of the pending danger. Our
research work further reassures us that a post-quantum
world is reassuringly similar to our current methods and
tactics
— Cryptography For A Post-Quantum Era, Thales eSecurity white paper
Crypto agility, then, must be a priority from this day forward.
Leaders in the Field
Cybersecurity firms like Thales eSecurity feel that what they are doing, and the way they are doing it, will be justified in the medium term. Post-quantum cryptography, they believe, must start now if it is to have a chance at protecting us against the advances that will surely come from quantum technologies.

By creating quantum-proof algorithms via a ‘crypto agility philosophy’ that can not only deal with quantum hacking but also handle the malware itself, quantum crypto attacks will be harmless, or at the very minimum, less devastating if they occur.
It is, however, imperative that countries with extensive research programs in quantum computing, as well as healthy private sectors in the industry such as the United States, Canada, China, Russia, and Europe, work together, utilizing a unitary, crypto-agile methodology, where harnessing the skills and intellects of everyone will be better for us all.